Third-Party Cookie Deprecation: Here’s What Privacy Teams Need to Know
Cookie deprecation didn't just disrupt marketing — it shifted the full burden of data governance onto enterprises collecting first-party data at scale. This guide covers what that means for consent infrastructure, AI pipelines, and privacy architecture.

Key Takeaways
Key Takeaways
- The ongoing third-party cookie deprecation is more than just a marketing disruption; it has turned into a fundamental infrastructure and data governance crisis for the enterprise.
- Shifting to first-party data transfers the burden of legal compliance directly to the organization. Every piece of ingested data must be backed by explicit consent.
- Consent management is a full-stack infrastructure challenge; capturing preferences at the browser level is useless if those signals fail to synchronize across every downstream system,
- Poor data governance introduces severe risks when feeding first-party data into AI systems, as models trained on unconsented data creates complex compliance liabilities.
- To survive this shift, organizations must deploy privacy-first architectures that automate data lineage, unify privacy taxonomies, and enforce real-time consent directly within the data layer.
For more than a decade, enterprises ran their digital marketing programs on what seemed like a rented logistics network. They owned neither the roads nor the trucks but reaped the benefits. They relied on a sprawling network of third-party couriers to gather intelligence: cookies, pixels, and external data brokers.
The system worked because it outsourced the complexity and the regulatory risk to external vendors. Gradually, the rules changed.
Driven by changing user expectations, regulators and browsers pulled the plug on the network of data highways, making third-party cookie deprecation a reality. In the current situation, old assumptions no longer work. Data pipelines have broken, and user data is vanishing.
In a rush to adapt to this data loss, organizations are building a first-party data strategy from scratch—bringing collection in-house through loyalty apps, direct channels, and gated content that now flood the enterprise with data.
But doing so exposes a critical flaw: most enterprises lack the infrastructure to govern it.
Consent is captured at the client side, but gets lost in the backend database. Unverified data flows into new systems, creating liabilities. Nothing seems broken until regulators knock, asking whether the data used is consented to by its owner.
Cookie deprecation is no longer just a marketing problem. It is an infrastructure crisis that falls directly onto the shoulders of privacy teams, data governance leaders, and platform engineers.
Surviving this transition requires building a privacy-first architecture. Defining how data is ingested, governed, and orchestrated must form the basis for enforcing consent across the enterprise network.
Although alternatives to third-party cookies have emerged, they won’t work if the foundation itself is on a fault line. So, why are organizations getting it wrong? And how are forward-thinking enterprises solving this issue directly at the root?
This article provides answers to these and other questions.
What is third-party cookie deprecation?
To understand the scale of this shift, we first need to answer the question: “What are third-party cookies and how do they differ from first-party cookies?”
First-party cookies are created and controlled by the host domain to maintain state and basic site functionality. For instance, it could be to keep a user logged in to their account or to remember items in the cart.
Third-party cookies, however, are client-side trackers injected by external domains—such as an ad network, analytics provider, or social media widget—to follow users across the web.
Data brokers and ad tech platforms leverage them to build user profiles, enabling cross-site tracking, behavioral advertising, and user identification across entirely separate domains.
The problem:
Engineering teams don’t control these cookies. They are created and used entirely outside of an organization’s centralized privacy infrastructure, creating severe data governance blind spots.
This model primarily outsourced three critical functions:
- Consent: Relying on third parties to validate user preferences.
- Lineage: Losing visibility into where data goes after it leaves the browser.
- Control: Allowing external brokers to dictate how user behavior is processed and monetized.
These blind spots go unnoticed until it’s too late. When regulators demand accountability, systems built on external trackers fail by design.
The solution: third-party cookie deprecation
To eliminate that vulnerability, the industry initiated third-party cookie deprecation, the systematic removal of tracking capabilities at the browser level. It is a policy shift in which the browser no longer accepts or sends cookies with a different domain attribute than the host, effectively rendering cross-site tracking, retargeting, and third-party attribution impossible.
The big picture:
However, the shift is systemic and extends beyond any single browser’s policies.
Even Forrester maintained this in the midst of unpredictable cookie deprecation updates: “As an industry, we are transitioning away from opaque consumer data collection and usage and toward a choice-driven, transparent, and privacy-friendly future.”
This is not simply a disruption to marketing strategies. It is a forced but necessary architectural reset. It compels organizations to replace obscure networks with internal, privacy-first infrastructure, driving the adoption of innovative, reliable, and transparent systems that enforce privacy from the inside out.
Why third-party cookies are losing relevance
Blocking third-party cookies by popular browsers isn’t the only reason organizations are seeking alternatives. As consumers increasingly opt out of cookies, global regulations tighten, and legal risk rises, third-party trackers are losing ground anyway.
Regulatory pressure from concerned authorities
Global privacy regulations, such as the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and evolving regional laws, weren’t designed merely to levy fines. They were set up to enforce a fundamental architectural principle: data minimization and explicit user consent.
By forcing enterprises to implement strict, affirmative-action consent models, regulators have effectively outlawed the silent data supply chain.
This theoretical risk has evolved into strict enforcement. Regulators are now actively auditing the underlying infrastructure:
- Financial reckonings: In late 2025, the French Data Protection Authority (CNIL) levied nearly half a billion euros in combined fines against major tech and retail platforms for deploying cookies without clear, prior user consent.
- Systemic sweeps: The European Data Protection Board (EDPB) just launched its Coordinated Enforcement Framework (CEF) for 2026, focusing on compliance with GDPR’s transparency obligations. The aim is to identify systems that fail to inform users how their data is processed.
Beyond penalizing individual trackers, regulators have made the invisible, cross-site collection of behavioral data legally and financially untenable, proving that the old model is no longer sustainable.
User behavior is accelerating the decline
Regulations require asking for permission, and most users respond with rejection.
When the tracking architecture is deprived of dark patterns and hidden menus, it collapses. Users are actively dismantling it across three fronts:
- Consent rejection: When given a clear “Reject all” option, 50% to over 60% of users opt out completely.
- Adblockers: Hundreds of millions bypass banners entirely by deploying adblockers to remove scripts before they load.
- Automated opt-outs: Protocols like Global Privacy Control (GPC) broadcast universal, automated opt-out commands.
The result: a massive data loss. Even if third-party cookies still function, they are losing both signal quality and legal defensibility.
Web browsers already block third-party cookies at scale
Third-party cookie deprecation isn’t a prediction; it's already happened.
While the industry fixated on Google Chrome’s shifting timelines, other major browsers dismantled cross-site tracking years ago:
- Apple Safari: Its Intelligent Tracking Protection (ITP) has blocked third-party cookies by default since 2020.
- Mozilla Firefox: Its Enhanced Tracking Protection (ETP) implemented default blocking in 2019.
- Privacy-first browsers: Browsers like Brave and DuckDuckGo reject external trackers out of the box.
Between default browser restrictions and widespread adblocker adoption, a massive share of all web traffic is already cookieless and completely invisible to legacy tracking.
Google’s reversal didn’t reverse the trend—it complicated it
In July 2024, Google abandoned the forced deprecation of third-party cookies in Chrome. Many businesses mistook this for a reprieve. However, rather than a complete reversal, it was a delegation.
Instead of adding a separate consent prompt, Chrome now allows users to manage cookie preferences directly in its “Privacy and security” settings. Google also clarified that Privacy Sandbox APIs will stay active alongside cookies.
The impact is operationally identical to a forced phase-out. Unsurprisingly, a vast number of users opt for enhanced privacy. The cookies are there, but restricted to a shrinking, consented audience.
The third-party cookie deprecation timeline
The industry spent years understanding what cookie deprecation is and anticipating a definitive end to third-party cookies, but the moment never arrived as a single event. In reality, cookie deprecation has unfolded as a series of drawn-out, fragmented events that gradually eroded signal quality.
Here’s how it played out in the last decade, including Google’s major cookie deprecation updates:
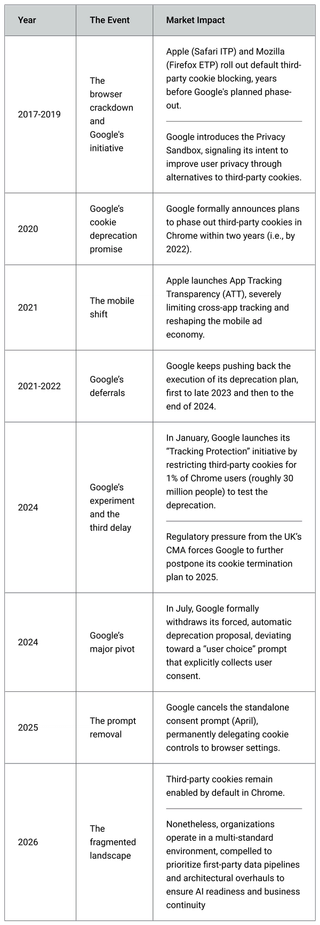
Today, there is no universal replacement for the third-party cookie. We are left with a fractured, hybrid environment. The transition never really ended; it simply became infinitely more complex.
Organizations waiting for a clean, industry-wide resolution are missing the reality. The cookieless future is not a single event, it is already here. Even with third-party cookies still functioning, rapid signal decay requires firms to upgrade their data infrastructure and enforce accountability internally.
The real problem: Cookie deprecation is a data governance crisis
The decline of the third-party cookie model is routinely framed as a marketing challenge. In reality, the true impact strikes at the core of data governance.
By fundamentally altering how personal data is stored and processed, deprecation disrupts more than ad targeting; it shifts the entire burden of legal compliance directly onto the enterprise.
This transition emphasizes the significance of consent management. As third-party trackers give way to a first-party data model, enforcing user preferences stops being a simple compliance formality to avoid fines. It now becomes a core operational requirement. If consent isn’t consistently applied across all digital systems and business units, the underlying data becomes functionally and legally useless.
First-party data comes with first-party liability
As external signals lose their value, organizations naturally rush to amass first-party data. They launch loyalty programs, gated content, and D2C pipelines to rebuild their targeting capabilities. While capturing this data solves the immediate operational gap, doing so without a robust governance infrastructure introduces severe legal exposure.
In the legacy approach, compliance risks were largely absorbed by a vast network of external vendors. Today, when an enterprise ingests user data directly, it assumes total, unavoidable liability. Every piece of first-party data must be backed by consent that is:
- Explicitly captured
- Securely stored
- Continuously enforced
- Easily retrievable to scale DSR (Data Subject Requests) fulfillment, and
- Fully auditable across all downstream systems.
Most current marketing infrastructures were designed solely for data collection and routing, making them ill-equipped for this level of rigorous privacy enforcement.
Consent is not a banner; it is an infrastructure problem
Organizations often treat privacy as a front-end user experience issue, but it is a deep infrastructure challenge. Capturing a user’s preference at the browser level means nothing if that signal fails to propagate across the internal tech stack.
Consent usually breaks down as data moves deeper into the enterprise. A single opt-out must instantly synchronize across multiple layers to prevent large-scale compliance failures:
- Data warehouses: Segregating unconsented data from compliant records.
- CRMs: Freezing automated outreach to users who rejected processing.
- Analytics and marketing tools: Preventing campaign activation based on obsolete permissions.
Relying on manual updates for consent management does not scale. True consent demands automated, real-time enforcement.
When front-end tracking and back-end governance are misaligned, the penalties are severe. Here’s an eye-opening example:
In a landmark 2023/2024 case, the Federal Trade Commission (FTC) levied a $25 million settlement against telemedicine provider GoodRx. The company’s stated policy promised never to share personal health conditions with advertisers. However, their underlying infrastructure told a different story: third-party tracking pixels embedded on their site were quietly routing sensitive user interactions directly to Meta and Google without user consent. It proved that a privacy policy is useless if the underlying system is actively bypassing it.
Cross-system identity resolution gets more fragile
Stripped of persistent external trackers, companies now rely heavily on internal identity graphs to recognize users across touchpoints. While these unified profiles are essential for maintaining operations, they create massive, centralized compliance vulnerabilities.
Internal identity resolution must be subjected to the same rigorous governance as any external data collection. The enterprise must enforce strict data minimization, automate retention schedules to purge stale records, and apply granular access controls. Operating an identity graph without these architectural safeguards transforms a valued business asset into a legal liability.
Attribution and measurement demand new governance models
To survive ongoing signal loss, organizations pivot to aggregated and modeled attribution. These statistical models are designed to bridge the visibility gap.
However, a model is only as sound as its foundation.
Modeled attribution demands flawless, auditable data. Inaccurate, incomplete, or unsynced consent records compromise the resulting insights. Weak privacy governance at the point of collection guarantees unreliable, legally questionable measurements downstream.
AI amplifies every governance gap
The scramble to replace the third-party cookie is colliding directly with the enterprise rush toward AI. These are not isolated initiatives.
Organizations that feed poorly governed first-party data into predictive models risk unpleasant compliance surprises. Once an AI system consumes and trains on unconsented data, identifying and extracting that specific information is nearly impossible.
Cookie deprecation has evolved beyond a web tracking issue. It is now a fundamental test of AI data readiness, requiring a fully governed, accountable supply chain from capturing and processing to expulsion. Embedding an AI governance platform like Astralis into this architecture helps automate that accountability, ensuring that only consented and verified data is ever provided to AI models.
Evaluating the emerging alternatives to third-party cookies
The industry is actively deploying workarounds to replace legacy tracking. However, these are evolving solutions, not 1:1 replacements for the existing ecosystem.
To maintain visibility, organizations are investing in a blend of the following approaches:
- Google Privacy Sandbox in 2026: While Google has retired some Privacy Sandbox features (such as attribution reporting API, IP protection, Topics API) due to “low levels of adoption”, it will continue to focus on secure, privacy-preserving measurement (interoperable attribution) and privacy-first identity authentication (FedCM and CHIPS) rather than direct ad targeting.
- Data clean rooms: These secure, encrypted environments enable brands and publishers to safely match their first-party datasets and derive aggregated insights without exposing underlying personally identifiable information (PII).
- Server-side tracking: By moving data processing from the user’s browser (client-side) to its internal servers, the organization gains strict, centralized control over which data points are routed to external vendors.
- First-party identity graphs: Companies are leveraging authenticated user data (logins, purchase histories) to build persistent, internal identifiers that do not rely on fragile external cookies.
- Contextual and zero-party data: As cross-site profiling continues to decline, brands are returning to contextual targeting (aligning ads with page content) and explicitly asking users for their preferences (zero-party data) to drive compliant personalization.
While these alternatives help bridge the signal gap for necessary measurement and targeting, they share one absolute dependency: a legally watertight data governance foundation.
Whether an enterprise uses data clean rooms or routes signals server-side, consent orchestration isn’t optional today.
With the enforcement of the EU AI Act and the rapid adoption of ISO 42001 (the international standard for AI management systems), regulators are actively scrutinizing the data pipelines that feed these models.
How mature enterprises build privacy-first data infrastructure
“For privacy and security teams, the challenge in 2026 is to do more with less - by rethinking data management through a risk-first lens. Teams are consolidating tools and clarifying ownership, focusing on what matters most. With better visibility into where sensitive data lives, how it is used and who or what can access it - including AI and non-human actors, organizations can reduce complexity and maintain control as data volumes grow and budgets remain constrained.”
- Security Brief, Australia (AI outpaces data privacy, exposing governance gaps)
To put it into action, a privacy-first data infrastructure should be designed for execution, not just compliance documentation. Instead of viewing cookie deprecation as a marketing issue, mature enterprises need to promote cross-functional collaboration among privacy, engineering, and data teams at the core, integrating controls directly into the data layer.
Privacy architecture will actually work in enterprise environments only when data is governed at the source and consent is enforced at the system level:
Step 1: Automate data inventory and lineage
You cannot govern data you cannot see. Static data maps and manual spreadsheet tracking collapse in large-scale, dynamic enterprise operations. Effective privacy management requires continuous visibility into where sensitive data lives and how it moves. Implementing a dynamic mapping tool like Helios can establish this foundational visibility natively within the data stack, replacing manual bottlenecks.
Organizations must:
- Deploy continuous discovery across cloud warehouses, SaaS applications, and unstructured stores to maintain a living map of the enterprise data ecosystem.
- Leverage AI-assisted classification to automatically tag PII with appropriate categories (personal, financial, and medical records) as it enters the pipeline, eliminating operational drag.
- Map end-to-end lineage to visualize exactly how sensitive data flows from the initial point of collection to downstream systems and AI models.
Step 2: Establish a unified privacy taxonomy
Governance fails when legal, engineering, and product teams speak different languages. Fragmented terminology across disparate tools creates massive compliance risks. Enterprises must establish a shared data language so all teams operate from a single, centralized source of truth.
This requires normalizing consent labels across the stack. For example, an “opt-out” in a marketing platform must map perfectly to “unsubscribed” in the CRM. By treating privacy definitions like software code and version-controlling them, taxonomy updates can propagate universally without breaking downstream systems when 2026 regulations shift.
Step 3: Orchestrate consent in real time
Consent is not a UI banner; it is a critical data routing dependency. Relying on delayed batch updates to manage user preferences risks consent gaps. To solve this, organizations must decouple consent from business logic by implementing a centralized permissioning layer that evaluates data events in real time.
Use automated webhooks and APIs to instantly push a user’s rejection to all downstream tools, preventing unauthorized data activation. Architect a failsafe so that if an event lacks a clear, verifiable consent signal, the system defaults to blocking the data flow to AI pipelines.
Here’s how it works in practice:
When a user selects opt-out on a web property, the architecture must instantly:
- Trigger a webhook that updates the global preference center in your CRM (e.g., Salesforce).
- Pause active outreach sequences in your marketing automation tools (e.g., Marketo).
- Segregate or purge the user’s unconsented behavioral data resting in your data warehouse (e.g., Snowflake).
Step 4: Embed controls directly into the data layer
Privacy must operate where data actually lives. Attempting to enforce rules through siloed compliance portals introduces drift between policy and practice.
Transition away from reactive portals by writing privacy rules directly into the underlying structure. By executing dynamic Attribute-Based Access Control (ABAC), data access is automatically restricted based on granular context such as user role, consent status, and intended processing purpose.
When policies are machine-readable and enforced by default, the system continuously generates defensible audit trails, eliminating the last-minute scramble for evidence during regulatory audits.
How Ethyca turns privacy into enforceable infrastructure
Enterprises can’t operate without meaningful data. The third-party cookie crisis has stripped them of reliable insights and quality signals.
To clear the confusion, enterprises turn to zero- and first-party data. But managing vast amounts of personal and sensitive data demands a rock-solid foundation. Without it, data leaks from cracks that teams don’t even know exist.
Ethyca helps enterprises mitigate this operational risk.
Trusted by 200+ global brands and processing 744M+ preferences annually, Ethyca offers end-to-end data governance solutions, from data inventory and codification of privacy policies to system-level consent enforcement.
It enables you to:
- Build a real-time map of where data is stored and how it moves.
- Centralize consent management across all enterprise units and systems.
- Translate front-end user preferences into automated backend commands.
- Develop a privacy-by-design architecture that prevents unconsented data from poisoning AI models.
- Generate defensible, continuous audit trails, instantly proving compliance to regulators.
Privacy management is an engineering discipline. Speak with Ethyca’s team to learn how to design a privacy engine from the bottom up.
.png?rect=534,0,2133,2133&w=320&h=320&fit=min&auto=format)

.png?rect=534,0,2133,2133&w=320&h=320&fit=min&auto=format)
_%20Why%20It%20Matters%20and%20How%20to%20Do%20It%20Right_Ethyca.png?rect=534,0,2133,2133&w=320&h=320&fit=min&auto=format)

.png?rect=0,3,4800,3195&w=320&h=213&auto=format)
.png?rect=0,3,4800,3195&w=320&h=213&auto=format)